Entitlement-Based Access Control Model
The JustineLonglaT-Lane platform uses an entitlement-based access control model to protect platform resources, APIs, runbooks, and premium tooling. Access decisions are based on a combination of user role, subscription tier, and required entitlements.
Access control flow diagram
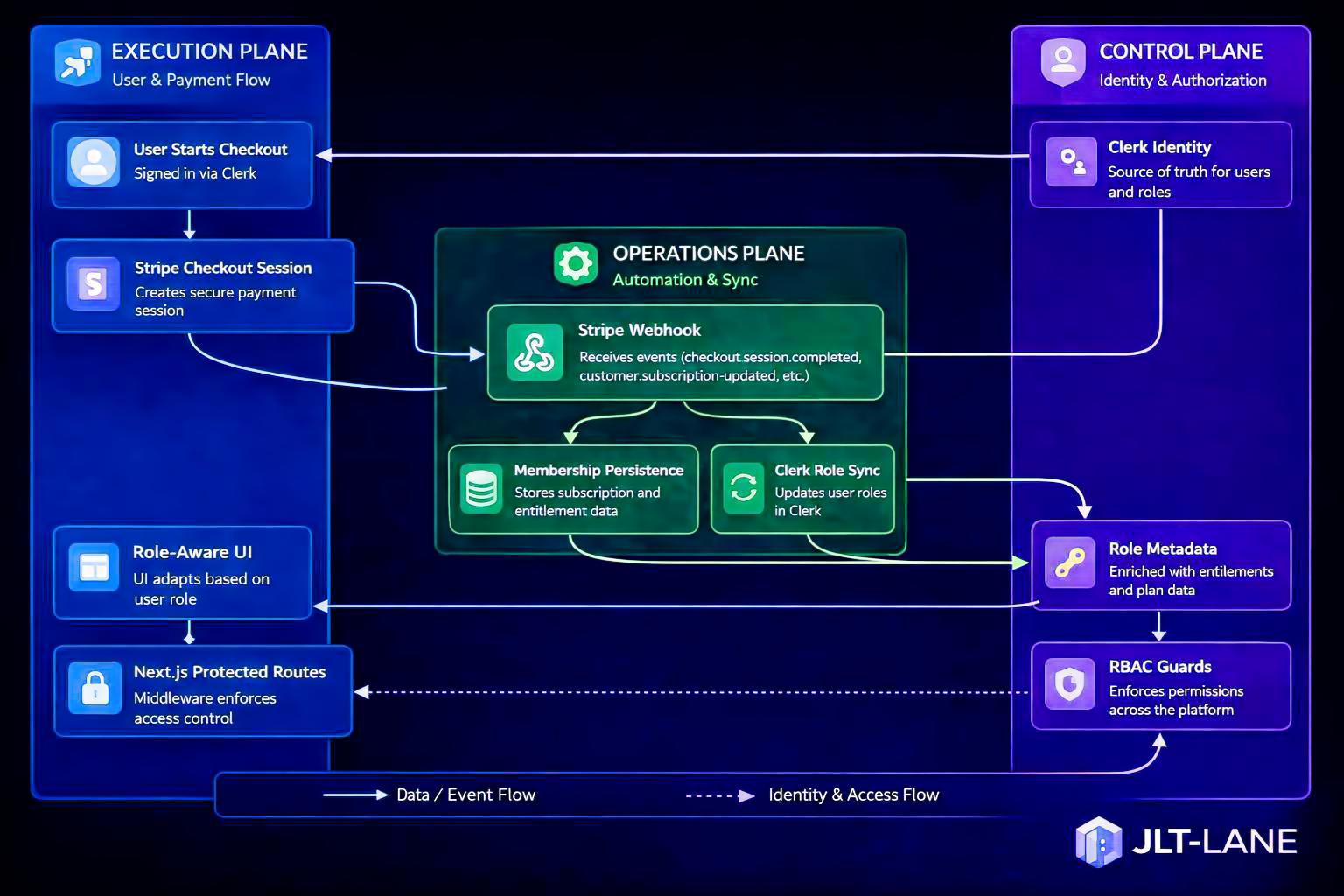
This diagram shows how billing and access control are unified into a single platform flow.
1. Identity Context
Every request is evaluated using an Identity Context, which represents the user and their platform role.
{
userId: string;
role: JltRole;
status: "active" | "inactive" | "suspended";
}Example roles include:
- public_visitor
- guest_contributor
- basic_member
- toolkit_subscriber
- platform_subscriber
- advisory_client
- admin
- owner
2. Subscription Context
The Subscription Context represents the user's subscription tier and status. This will later be connected to Stripe for billing and subscription management.
{
tier: "none" | "starter" | "toolkit" | "platform" | "advisory" | "internal";
status: "active" | "inactive" | "trial" | "expired";
}3. Authorization Profiles
Authorization profiles are defined in config/access-model.json.
Each role maps to a profile that defines:
- Subscription tier
- Entitlements
- Allowed resource groups
- Denied resource groups
{
"authorizationProfiles": {
"public_visitor": {
"subscriptionTier": "none",
"entitlements": [],
"allow": ["docs.public", "runbooks.public"],
"deny": ["docs.private", "runbooks.private"]
}
}
}4. Resource Groups
Resources in the platform are grouped into logical Resource Groups. Access is granted or denied at the resource group level.
- docs.public
- docs.private
- runbooks.public
- runbooks.private
- toolkit.preview
- toolkit.full
- automation.templates.basic
- automation.templates.premium
- api.platform.read
- api.platform.execute
- api.admin
- billing.customer
- billing.admin
- contributor.protocols
5. Access Evaluation Flow
Request
↓
API Route
↓
Session Context
↓
Access Profile
↓
Entitlement Check
↓
Allow / Deny
↓
Response (200 or 403)6. Protected Routes Example
const denied = requireEntitlement(
context,
"contributor.protocols",
["contributor.protocol.read"]
);
if (denied) return denied;If the user does not have the required entitlement, the API returns a 403 Forbidden response.
7. Platform Architecture Role
This access control system is part of the platform's Control Plane and is responsible for:
- Protecting premium platform features
- Controlling access to runbooks and automation templates
- Enforcing subscription-based feature access
- Securing platform APIs
- Supporting contributor and member access levels
Related: Access Model · Architecture Map
Related files:
/config/access-model.json
/lib/authz/profiles.ts
/lib/authz/evaluate-access.ts
/lib/authz/require-entitlement.ts
/lib/authz/session-context.ts

