One System, Not Two
Instead of handling billing and authorization as separate concerns, this architecture treats payment as part of the platform control path.
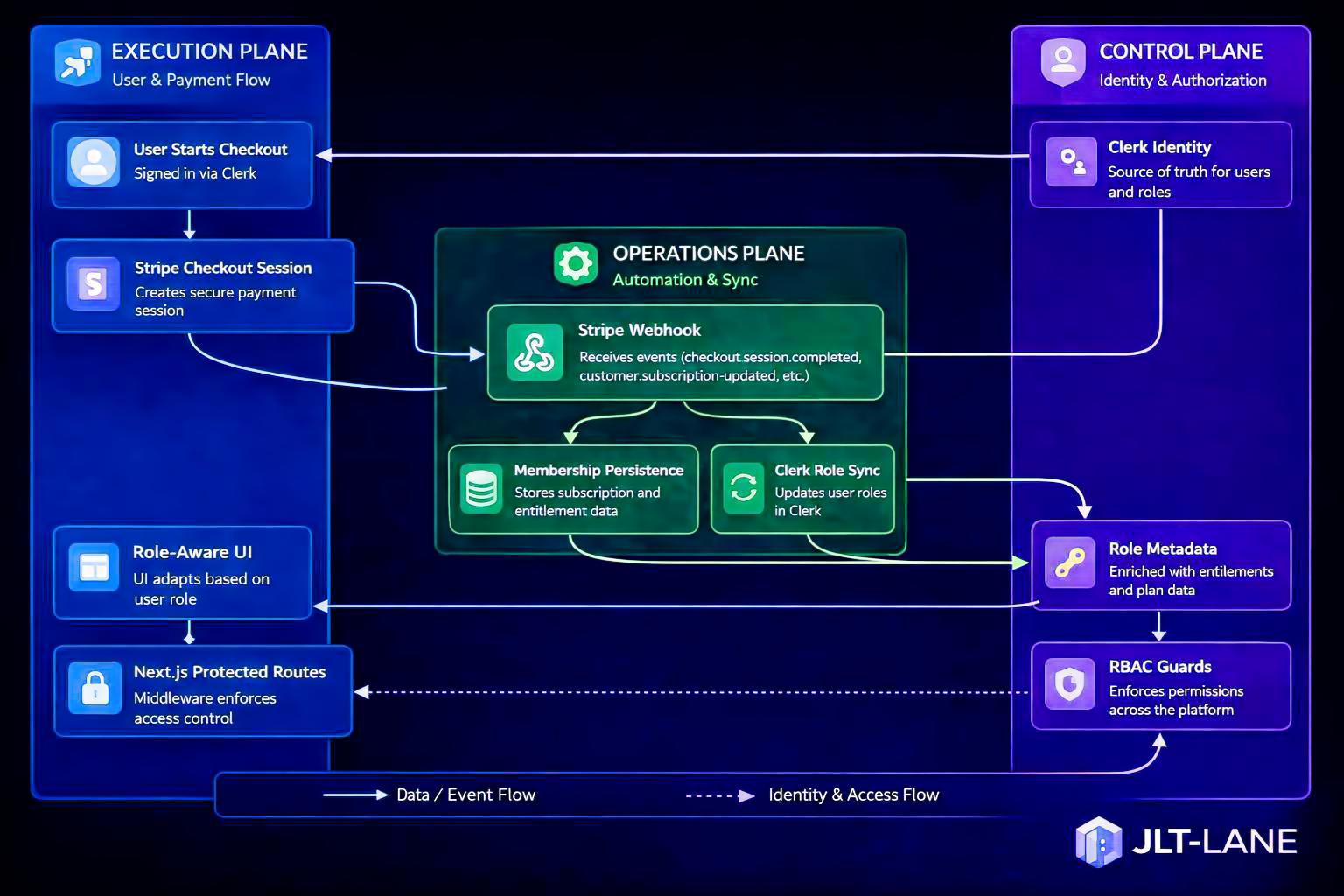
Platform Architecture
Connecting identity, billing, and access control as one governed platform flow.
“I stopped treating billing and access control as separate systems. I designed them as one.”
This page documents how JLT-Lane connects Clerk identity, Stripe checkout, webhook automation, role metadata, and RBAC enforcement into one clear system model.
The entitlement flow spans three platform planes: execution, operations, and control. The execution plane captures user and payment actions, the operations plane processes webhook automation and synchronization, and the control plane maps entitlements to access decisions enforced across the platform.
“I stopped treating billing and access control as separate systems. I designed them as one.”
At a high level, the system turns a payment event into an access-control event.
Instead of handling billing and authorization as separate concerns, this architecture treats payment as part of the platform control path.
When the payment state changes, the platform can update roles and access automatically without manual provisioning.
Entitlements are enforced through role metadata and RBAC guards, making platform access structured, auditable, and easier to reason about.
User & Payment Flow
The execution plane captures the user-facing flow. A signed-in Clerk user begins checkout, Stripe creates a secure checkout session, and the platform associates the payment action with user identity.
Automation & Sync
The operations plane receives and processes Stripe events. It persists membership and entitlement state, then synchronizes user role changes back into the identity layer.
Identity & Authorization
The control plane holds the identity and authorization model. Clerk remains the source of truth for users, role metadata maps plans to permissions, and RBAC guards enforce access across the platform.
Payment actions are associated with user identity early in the flow so downstream systems can update the correct account with confidence.
Plan and role information flows through controlled metadata rather than manual after-the-fact access changes.
The platform responds to entitlement changes through role-aware UI behavior and protected route enforcement.
This architecture reflects a platform mindset: identity, payment, automation, and authorization should not behave like disconnected systems. They should work together as one governed flow that is easier to operate, secure, and scale.
In this model, billing is not only a financial event. It is also a platform control event that directly shapes user access.